ZK Proof Generation Challenges on Smartphones for Verifiable Credentials Wallets

In the evolving landscape of decentralized identity, verifiable credentials wallets like ZKCredWallet are pushing the boundaries of privacy by leveraging zero-knowledge proofs (ZKPs) on smartphones. Yet, generating these ZK proofs on smartphones remains a formidable challenge, balancing computational limits with the promise of selective disclosure. Users expect seamless verification of attributes – age, nationality, or skills – without exposing underlying data, but mobile hardware strains under the cryptographic load.

The allure of zero knowledge proof mobile integration lies in empowering users with control over their digital selves. Imagine proving you’re over 21 for a DeFi loan or verifying professional credentials for a gig economy job, all without revealing your full identity. Sources from ScienceDirect and HashStudioz highlight how ZKPs mitigate blockchain privacy risks while enabling minimal exposure in identity wallets. However, as Zimperium’s mobile security glossary notes, performance bottlenecks, cryptographic tooling gaps, and UX friction stand in the way.
Resource Constraints Hampering ZK Proof Generation Time
Smartphones, despite their advancements, grapple with the intensive math behind ZKPs. Generating a proof involves elliptic curve operations, polynomial commitments, and recursive proofs in systems like SNARKs or STARKs. On devices with limited CPU, GPU, and RAM, this translates to delays that can stretch from seconds to minutes – unacceptable for real-time interactions.
ArXiv papers on lightweight mobile crypto wallets underscore the need for backend selection, like choosing Groth16 over Bulletproofs for efficiency. Yet, even optimized circuits demand significant power. Battery drain becomes acute; a single proof can consume 10-20% charge on mid-range Androids, per ongoing research. This impacts verifiable credentials wallet performance, turning a privacy boon into a usability deterrent. In my view, developers must prioritize hybrid approaches – offloading non-sensitive setup to the cloud while keeping proof finalization on-device – to sustain user trust.
Hardware Limitations and Secure Element Mismatches
The European Data Protection Supervisor points to a core issue: anonymous credentials often rely on signature schemes incompatible with smartphone secure elements. Apple’s Secure Enclave or Android’s StrongBox prioritize common curves like secp256k1, but advanced ZK schemes demand CL signatures or BLS, unsupported natively. This forces software-only implementations, vulnerable to side-channel attacks.
ZK Proof Hardware Challenges
-
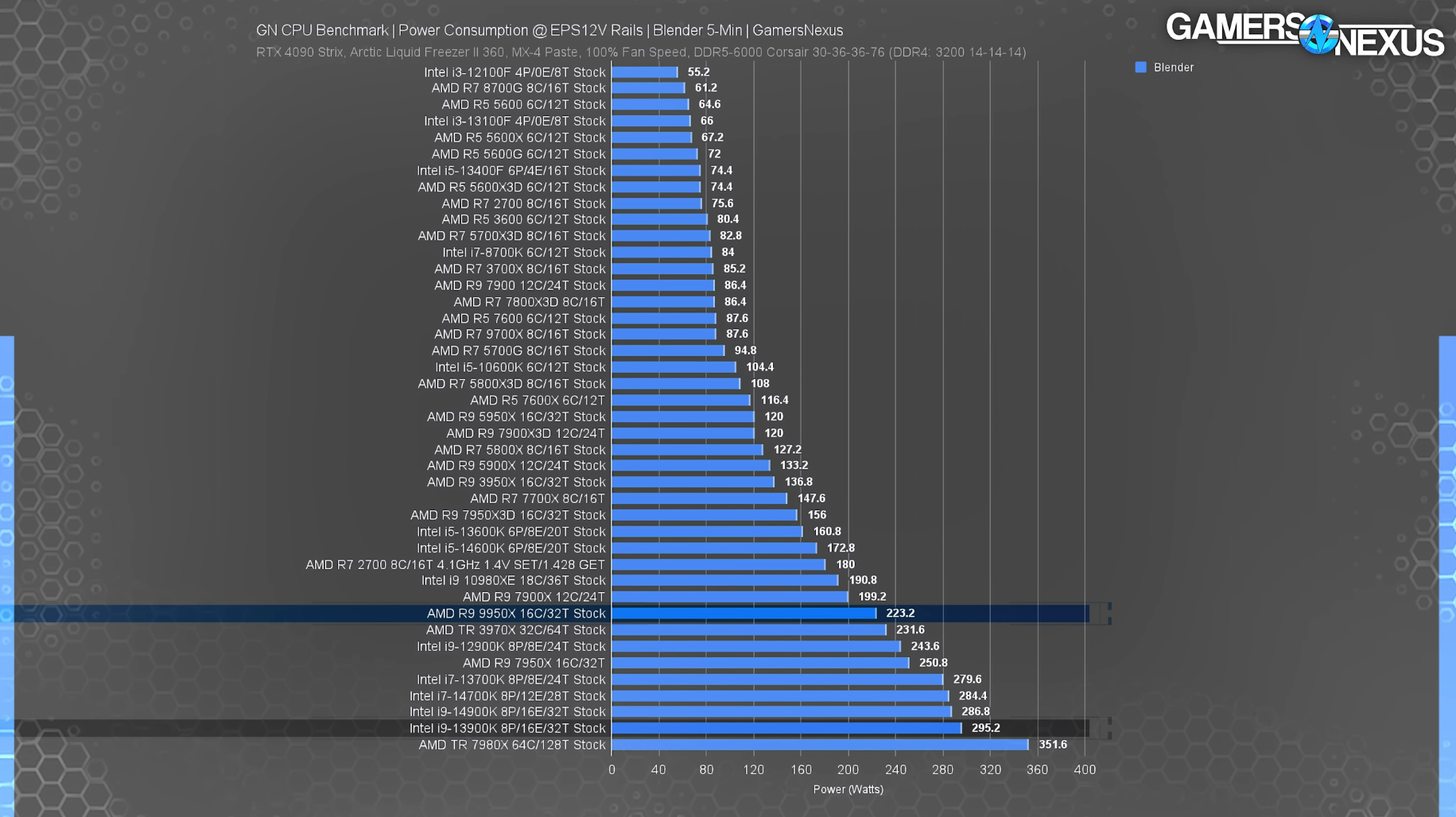
CPU Limitations: Mobile processors lack the raw power for intensive ZK proof computations, leading to slow generation times.
-
Secure Element Incompatibility: Hardware secure elements in phones don’t support required signature schemes for binding anonymous credentials.
-

Memory Constraints: Limited RAM hinders handling large intermediate values during proof generation on resource-strapped devices.
-

Battery Impact: High computational demands cause rapid battery drain, degrading user experience on smartphones.
Cryptology ePrint Archive designs for offline document wallets reveal workarounds, like binding proofs to hardware roots without full secure element reliance. Ethereum Research on passport-based ZK identity proofs echoes this, stressing uniqueness verification without full disclosure. For mobile ZK wallet optimization, integrating post-quantum primitives adds further overhead, as they balloon key sizes and computation. Balanced against quantum threats, it’s a necessary evolution, but one that demands silicon-level innovations from chipmakers.
Cryptographic Complexity Meets Everyday Use
Beyond raw compute, the diversity of ZKP families – from zk-SNARKs’ succinctness to Bulletproofs’ transparency – complicates wallet deployment. GitHub discussions on ZK proof schemes detail privacy properties, yet selecting the right one for mobile involves trade-offs in setup time, verifier costs, and revocation support. Privacy-friendly revocation, vital for credentials like skills badges from JFF reports, requires accumulator-based ZKPs that multiply proof sizes.
Deutsche Bank’s blockchain finance insights affirm ZKPs’ role in verifying data sans revelation, but on phones, this sophistication risks alienating non-technical users. MIT Solve’s phoneless wallets vision hinges on tamper-proof VCs, yet generation hurdles persist. Here, ZK proof generation time isn’t just technical; it’s a barrier to adoption in skills-first talent markets.
Usability demands simplicity, yet ZK proof generation on smartphones often confronts users with progress bars that linger too long or cryptic error messages when proofs fail due to thermal throttling. Non-technical individuals, the bulk of potential adopters in talent marketplaces, need interfaces that demystify selective disclosure – showing exactly what attribute is proven, like “over 21” without age specifics. Wallet apps must bridge this gap, abstracting circuit compilation and proof recursion into one-tap experiences.
Comparison of ZKP Schemes for Smartphones
| Scheme | Proof Generation Time (ms on mid-range smartphone) | Proof Size (KB) | Verifier Time (ms) | Mobile Suitability |
|---|---|---|---|---|
| Groth16 | 150-350 | 0.3 | 3-10 | High ⭐⭐⭐⭐⭐ |
| Bulletproofs | 2,000-5,000 | 1.5-3 | 50-150 | Medium ⭐⭐⭐ |
| PlonK | 500-1,500 | 1-2 | 10-40 | High ⭐⭐⭐⭐ |
Revocation mechanisms add another layer of intricacy. As the updated research from 2026 underscores, privacy-preserving revocation for credentials demands accumulators or vector commitments, inflating proof sizes and generation times. On resource-strapped devices, this can push ZK proof generation time beyond practical limits, especially for dynamic lists like revoked skills badges. Developers face trade-offs: efficiency versus unlinkability, where repeated proofs risk correlation attacks if not randomized properly.
Overcoming Barriers: Innovations in Mobile ZK Wallet Optimization
Progress is underway. Researchers advocate general-purpose ZKPs compatible with any signature scheme, sidestepping secure element mismatches noted by the European Data Protection Supervisor. These schemes, built on polynomial IOPs, run within mobile computational envelopes, targeting under 5-second proofs on flagship devices. Post-quantum integrations, though hefty, leverage lattice-based proofs like Dilithium for signatures, paired with ZK wrappers for forward security.
zkSync Technical Analysis Chart
Analysis by David Patel | Symbol: BINANCE:ZKUSDT | Interval: 4h | Drawings: 6
Technical Analysis Summary
To illustrate this bearish chart for ZKUSDT in my balanced hybrid style, start by drawing a primary downtrend line connecting the swing high on 2026-01-05 at 0.1200 to the recent low on 2026-02-09 at 0.0850. Add horizontal support at 0.0800 and resistance at 0.1000 and 0.1200. Mark a consolidation rectangle from 2026-01-20 to 2026-02-01 between 0.0900 and 0.1100. Use arrow_mark_down on the MACD bearish crossover around 2026-01-25, and a callout on declining volume post-breakdown. Place long entry zone at 0.0820-0.0850 with stop below 0.0800 and profit target at 0.1050. Add text notes for risk-managed hybrid view: ‘Fundamentals strong on ZKP adoption, but await technical confirmation.’ Use fib_retracement from recent low to prior high for potential retrace levels.
Risk Assessment: medium
Analysis: Bearish technical structure with downtrend intact and declining volume, offset by strong ZKP fundamentals and support test; medium tolerance suits defined risk entries
David Patel’s Recommendation: Cautious long bias at support with tight stops, scale in on confirmation; diversify with forex hedges for balance
Key Support & Resistance Levels
📈 Support Levels:
-
$0.08 – Strong multi-touch low from late Dec/Jan volume shelf, key hold level
strong -
$0.09 – Intermediate support from consolidation base
moderate
📉 Resistance Levels:
-
$0.1 – Recent breakdown level, prior consolidation top
moderate -
$0.12 – January swing high, major resistance zone
strong
Trading Zones (medium risk tolerance)
🎯 Entry Zones:
-
$0.083 – Bounce from strong support 0.0800 with potential bullish MACD divergence, hybrid buy on ZKP news catalyst
medium risk -
$0.095 – Break above minor resistance on volume increase for add-on
low risk
🚪 Exit Zones:
-
$0.105 – Initial profit target at next resistance
💰 profit target -
$0.078 – Tight stop below key support to limit downside
🛡️ stop loss -
$0.12 – Stretch target at major resistance
💰 profit target
Technical Indicators Analysis
📊 Volume Analysis:
Pattern: declining post-spike
High volume on initial drop from highs, now fading on downside confirming distribution over accumulation
📈 MACD Analysis:
Signal: bearish crossover with histogram contraction
MACD line crossed below signal in late Jan, momentum fading but watch for divergence at lows
Applied TradingView Drawing Utilities
This chart analysis utilizes the following professional drawing tools:
Disclaimer: This technical analysis by David Patel is for educational purposes only and should not be considered as financial advice.
Trading involves risk, and you should always do your own research before making investment decisions.
Past performance does not guarantee future results. The analysis reflects the author’s personal methodology and risk tolerance (medium).
Hybrid models emerge as pragmatic fixes. Pre-compute trusted setups off-device, then finalize proofs locally; this slashes on-phone compute by 70%, per arXiv benchmarks on lightweight wallets. For verifiable credentials wallet performance, hardware accelerations like ARM’s Confidential Compute Architecture promise GPU-accelerated elliptic curves, natively supporting BLS operations. ZKCredWallet exemplifies this shift, embedding optimized circuits for common verifications – age gates, KYC-lite, credential portability – while monitoring battery via adaptive proof recursion.
In my assessment, balancing these elements requires developer maturity, as JFF reports on VC wallets observe. Focus has pivoted to demos: real-world pilots proving skills in gig platforms without data leaks. Yet, open standards like those from Ethereum Research for passport ZKPs are crucial; proprietary circuits stifle interoperability.
Building Trust and Scaling Adoption
Trust hinges on transparency. Users must grasp what zero knowledge proof mobile entails – no data leaves the device, verifiers learn nothing extra. Audits, community bounties, and clear UX flows counter skepticism. Education campaigns, drawing from Zimperium’s glossaries, can normalize concepts like succinct proofs, fostering uptake in DeFi and beyond.
Scalability beckons with STARKs’ quantum resistance and transparency, minus SNARKs’ trusted setups. Though verifier-heavy, recursive aggregation compresses chains for mobile. Deutsche Bank’s finance lens reveals ZKPs’ verification power; extend this to smartphones, and wallets become ubiquitous identity hubs. Challenges persist – thermal runaway during batch proofs, intermittent network for revocation checks – but iterative gains point to viability.
ZKCredWallet stands at this frontier, optimizing ZK proof smartphone generation through profiled circuits and user-centric metrics. Battery-aware scheduling, proof caching for repeated claims, and fallback to QR-code relays ensure resilience. As silicon evolves and algorithms refine, the friction dissolves, unlocking privacy as default in Web3 identities. Developers prioritizing these facets will lead, turning hurdles into competitive edges for sustainable, trustless ecosystems.









