ZK Proofs vs Validity Proofs in Verifiable Credentials Wallets for Web3 Privacy 2026

In 2026, Web3’s privacy frontier hinges on verifiable credentials wallets that leverage ZK proofs and validity proofs to shield user data amid booming DeFi and decentralized identity ecosystems. These cryptographic tools let you prove you’re over 21 for a loan without flashing your birth certificate, or confirm solvency for a trade without exposing your full portfolio. Yet, as adoption surges, the subtle distinctions between ZK proofs and validity proofs spark debate among developers and users alike. Understanding them is key to selecting the right zero knowledge wallet 2026 setup.

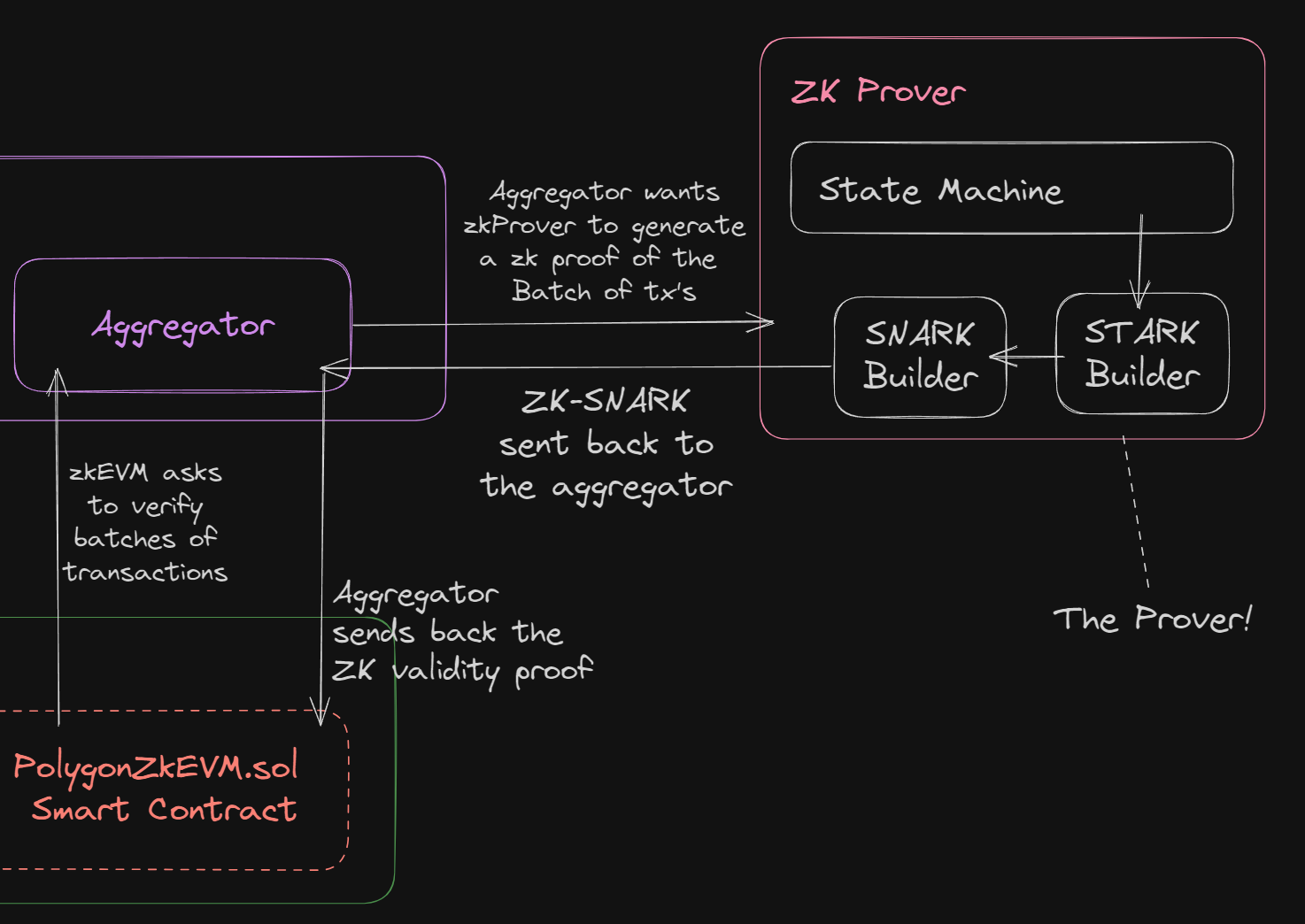
Zero-knowledge proofs emerged from theoretical cryptography in the 1980s but hit Web3 prime time with protocols like zk-SNARKs and zk-STARKs. At their core, ZK proofs allow a prover to convince a verifier of a statement’s truth, say “I hold credential X, ” without revealing X itself. This selective disclosure is a game-changer for verifiable credentials privacy Web3, aligning perfectly with W3C standards for decentralized identifiers (DIDs) and verifiable credentials (VCs). Imagine logging into a dApp, proving KYC compliance via Polygon ID-style tech, all without linking it to your on-chain history.
ZK Proofs in Action: Privacy Without Compromise
Wallets like ZKCredWallet integrate ZK proofs to generate attestations on-chain or off, verifiable via smart contracts. A user might prove attributes like “income above threshold” for a ZK credentials DeFi wallet interaction, drawing from sources emphasizing shielded transfers and pseudonymity-to-anonymity upgrades. This isn’t mere math; it’s practical empowerment. Polygon ID, for instance, uses ZK to authenticate without data leaks, fostering trustless yet private exchanges. But efficiency matters: zk-SNARKs offer compact proofs for mobile wallets, while zk-STARKs prioritize transparency, dodging trusted setups.
Key ZK Proof Benefits in VC Wallets
-
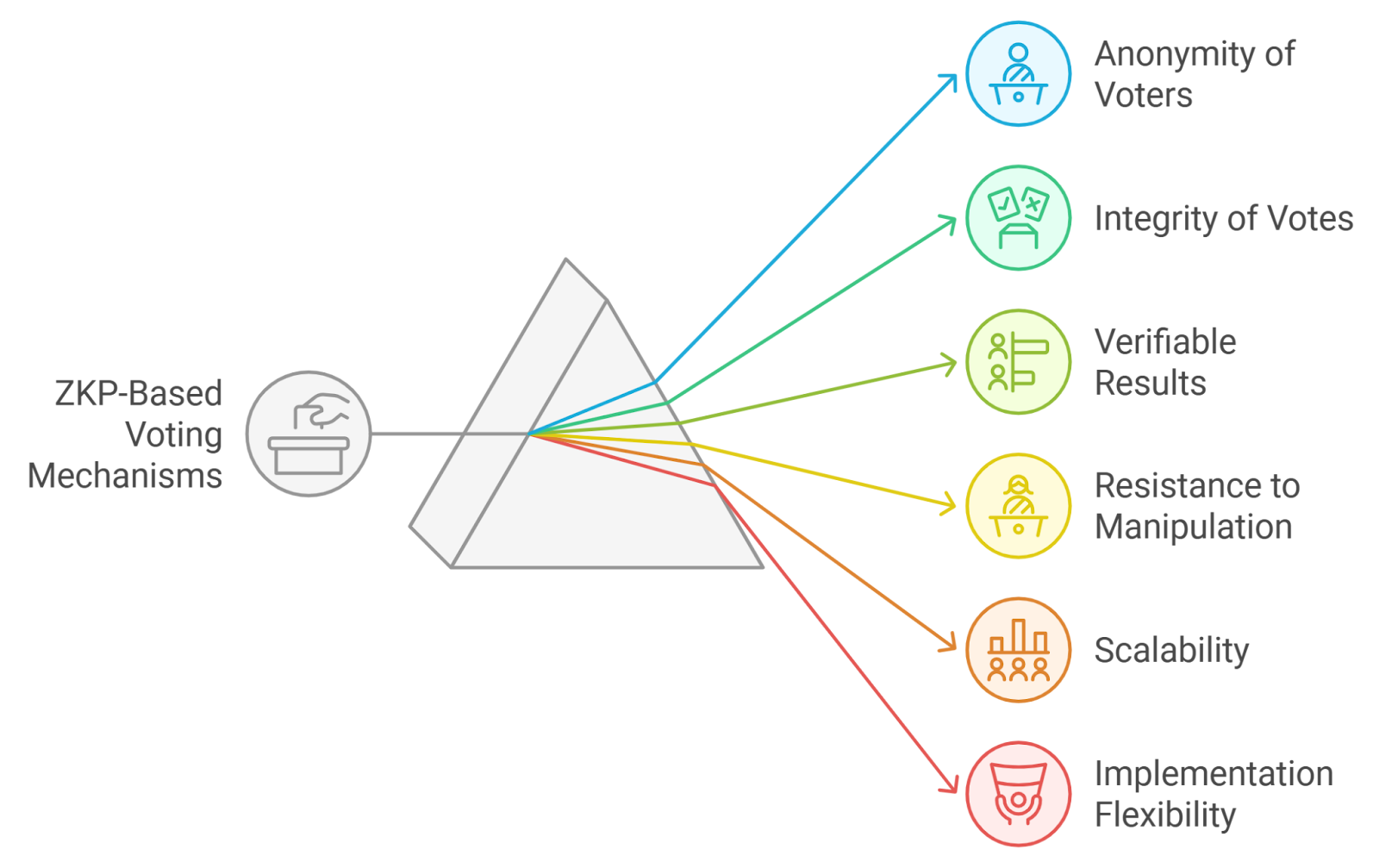
Selective Disclosure: Prove attributes like age >18 without revealing exact birthdate or other data, as in Polygon ID implementations.
-
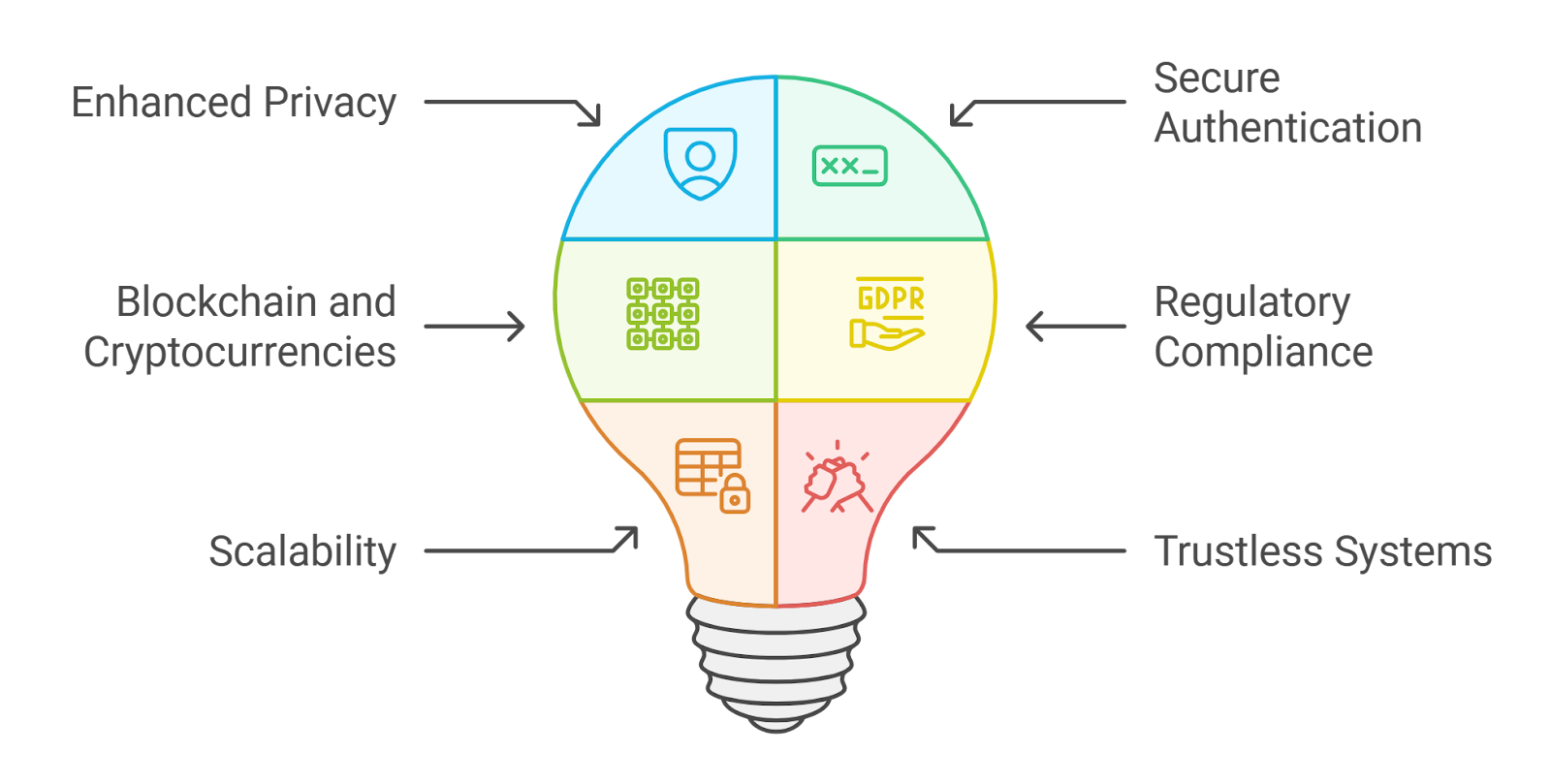
DeFi Scalability: Immediate transaction validation without data exposure, outperforming fraud proofs for efficient Web3 scaling.
-
GDPR Compliance: Enables privacy-by-design, sharing minimal data to meet regs like GDPR and W3C VC standards.
-
Quantum Resistance: Lattice-based ZK schemes provide potential post-quantum security for long-term VC wallet resilience.
-
DID Integration: Seamless with DIDs via Polygon ID, allowing secure, verifiable interactions without sensitive data leaks.
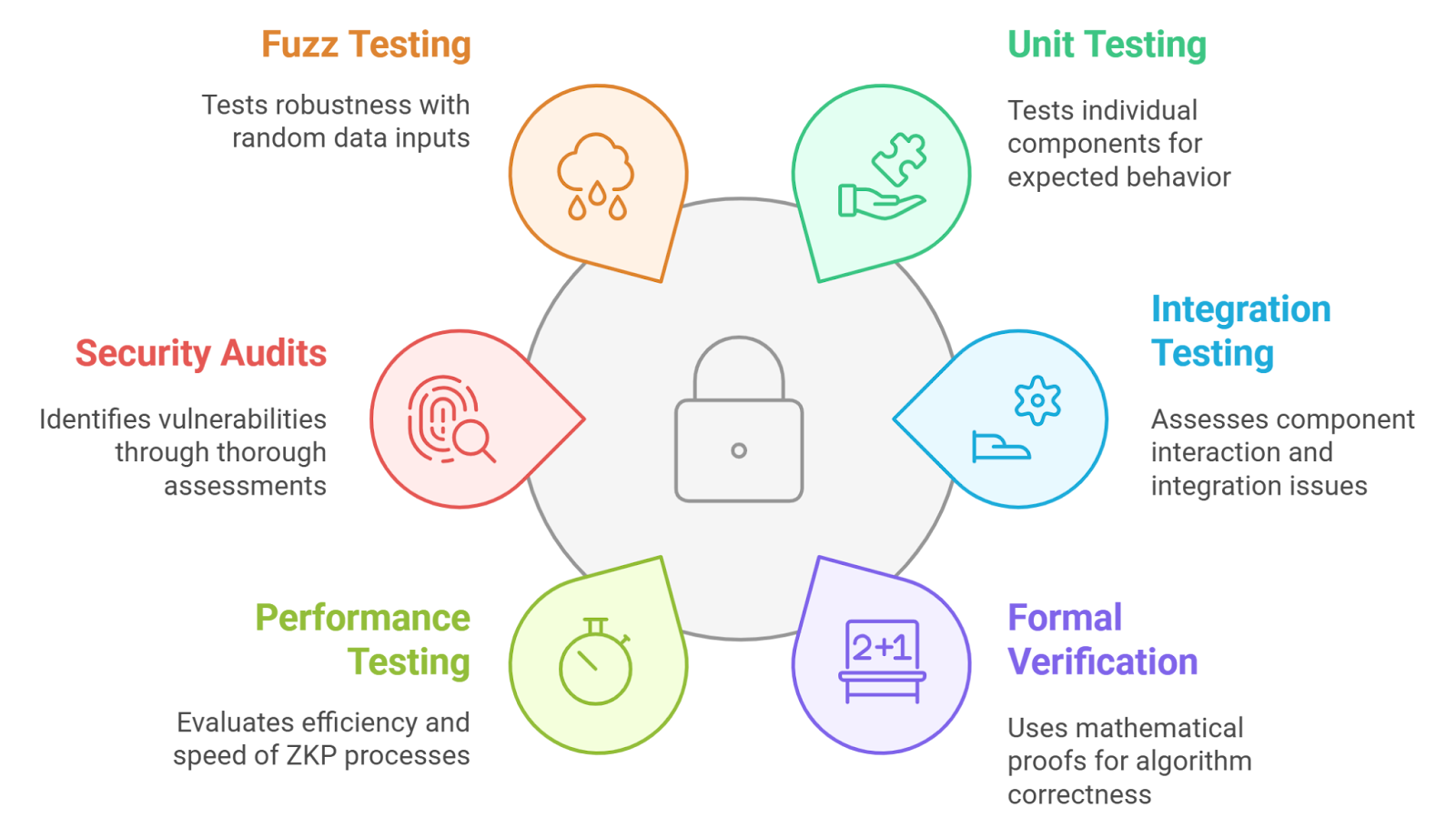
Critics point to proof generation’s computational heft, yet 2026 hardware optimizations and recursive proofs mitigate this, making ZK viable even on consumer devices. The result? Users dictate data flow, reversing Web2’s surveillance model.
Unpacking Validity Proofs: Beyond Basic ZK
Validity proofs, often a ZK subset, certify correct computation execution. Think general-purpose ZK: prove a program’s output without rerunning it. In VC wallets, they validate credential issuance or revocation logic on-chain, ensuring no tampering. Unlike fraud proofs, which challenge invalid states post-facto, validity proofs offer succinct, immediate verification; a transaction either checks out or fails upfront. Alchemy’s insights highlight this speed edge, crucial for high-throughput DeFi where delays kill trades.
For verifiable credentials privacy Web3, validity proofs shine in complex scenarios, like aggregating multiple VCs into a single proof for multi-party protocols. Mina Protocol’s lightweight blockchain exemplifies this, using ZK to recurse entire state proofs, slashing storage needs. Yet, they’re not interchangeable with pure ZK attribute proofs; validity leans toward program correctness, ZK toward data privacy.
Head-to-Head: ZK vs Validity in Wallet Ecosystems
Directly pitting ZK proofs verifiable credentials against validity proofs reveals nuanced trade-offs. ZK excels at minimal disclosure, ideal for user-facing wallets proving age or membership. Validity proofs dominate backend verification, assuring issuers and verifiers of protocol fidelity. In a validity proofs vs ZK wallet debate, hybrids win: wallets combine both for end-to-end security. For example, prove credential validity (ZK) and issuance process integrity (validity) in one flow. arXiv frameworks propose scalable DID-VC-ZKP stacks, blending them for privacy-preserving scaling. Onchain Passport details ZK’s role, underscoring wallet implementations that prioritize this synergy. Cost-wise, ZK proofs average lower gas on Ethereum L2s by 2026, but validity proofs scale better for rollups. Choose based on use case: pure privacy demands ZK; computational trust favors validity.
Hybrid approaches are gaining traction in leading wallets, where ZK proofs handle attribute verification while validity proofs secure the underlying computation. This duality addresses the validity proofs vs ZK wallet tension head-on, delivering robust defenses against both data leaks and protocol exploits. Developers favor this stack for its modularity; swap zk-SNARKs for STARKs as quantum threats loom, without overhauling validity layers.
Real-World Deployments: ZK and Validity in Leading VC Wallets
By 2026, wallets like ZKCredWallet exemplify this evolution, storing and verifying attestations via zero-knowledge proofs without exposing personal data. Users prove solvency in DeFi protocols or age for NFT drops, all through selective disclosure powered by ZK. Validity proofs underpin these operations, confirming credential circuits executed flawlessly on-chain. Polygon ID’s implementation, aligned with W3C VCs and DIDs, showcases how ZK enables trustless logins to dApps minus on-chain footprints. Mina Protocol pushes further, recursing validity proofs to keep blockchains feather-light, ideal for mobile zero knowledge wallet 2026 users juggling credentials across ecosystems.
ZK Proofs vs Validity Proofs in Verifiable Credentials Wallets
| Feature | ZK Proofs | Validity Proofs | Best For |
|---|---|---|---|
| Privacy Level | Maximal 🔒: Proves statements true without revealing underlying data (e.g., over 18 without birthdate) | High 🔒: Cryptographic assurance of truth without extra info | ZK for selective disclosure in Web3 identity |
| Computation Verified | ✅ Yes: Verifies attributes/claims via zk-SNARKs etc. | ✅ Yes: Specifically proves full computation correctness | Validity for off-chain execution in VCs |
| Gas Efficiency | Moderate-High: Prover-intensive but optimized in 2026 (e.g., Polygon ID) | High: Efficient for batched validations in rollups | Validity for scalable VC interactions |
| Use Case Examples | Age verification, shielded transfers, Polygon ID auth | VC issuance/revocation proofs, smart contract state transitions | ZK for pure privacy, Validity for verifiable computations |
Sources like CoinsBench and Dock Labs underscore ZK’s role in shielded transfers, extending to credentials where privacy meets verifiability. Yet, ont. io notes zk-SNARKs’ edge in blockchain security, balancing proof size against speed. In practice, a ZK credentials DeFi wallet might use validity proofs for multi-signature schemes, ensuring aggregated VCs from diverse issuers remain untampered.
Zero-knowledge proofs solve blockchain’s pseudonymity paradox, evolving it toward true anonymity in credential systems.
This isn’t hype; it’s deployed reality. Hiro. so highlights how ZK bridges public ledgers with private proofs, vital as regulations demand compliance without surveillance.
Wallets blending both, like ZKCredWallet, stand out for developers building DeFi frontends or identity layers. They enable seamless proofs of attributes like credit score ranges or professional certifications, fueling trustless economies.
Forward-looking, recursive ZK validity proofs will dominate, compressing entire histories into tiny verifiers. This empowers verifiable credentials privacy Web3 at hyperscale, from metaverses to tokenized assets. Users gain agency: control what verifiers see, when. Developers unlock composable privacy primitives. The shift favors thoughtful architectures over one-size-fits-all, rewarding early adopters with defensible moats in a data-hungry world. ZKCredWallet leads this charge, proving credentials without compromise.






